Judas: Phishing Resurrected
If you’ve been reading my blog since I started writing on Medium, you’ll remember Judas, the pluggable open-source phishing proxy. I wrote Judas to prove a point on an engagement once, and unfortunately neglected it afterwards. (Side note: Go’s comprehensive standard library makes it easy to toss together a proof of concept on an engagement). I’ve had a lot more time to write code in lockdown so I decided to show Judas some love.
What is Judas?
Judas is a pluggable reverse proxy for red team phishing engagements based on Go’s httputil.ReverseProxy. Simply point it at the target website, give it a domain for the SSL certificate and you’re on your way. Judas makes a byte-for-byte copy of the original requests and responses making it impossible to tell the difference between a phishing site and the original without checking the URL bar. Victims will be able to log into the target and use it like they normally do.
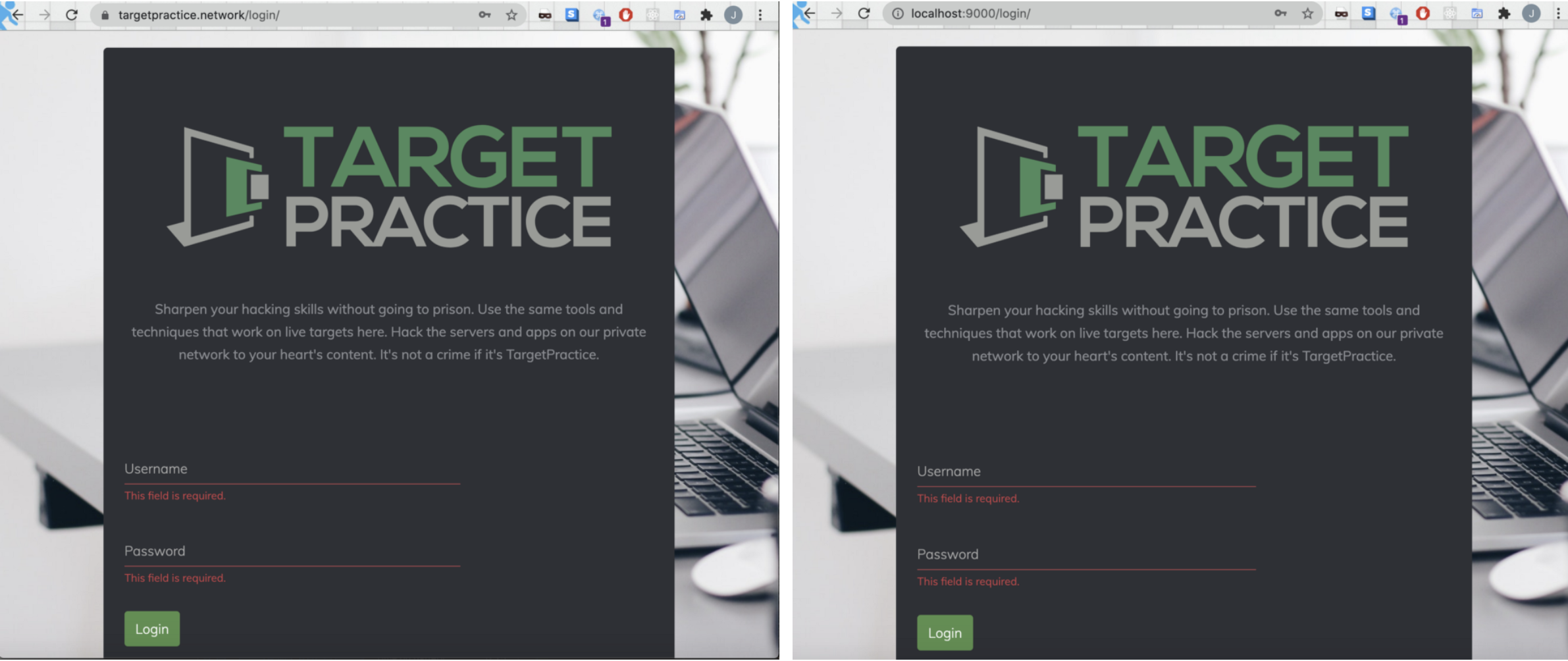
Judas cloning targetpractice.network on localhost:9000.
(I own targetpractice.network, don’t use Judas on websites you don’t have permission to attack).
This is made possible by supplying functions for the ReverseProxy struct that rewrite requests and responses on the fly. ReverseProxy is versatile: you can use it to build Web Application Firewalls, patch vulnerabilities in services you can’t update and much more. It’s worth adding to your toolkit no matter which team you’re on.
Stealth Goodies
Judas comes with some features to help us hide from the target server and victims. We want to stay hidden from the blue team as long as possible to increase our chances of compromising a high value account.
Automatic Let’s Encrypt
We’ve spent the last few years conditioning people to trust that padlock in their URL bar. Thanks to Let’s Encrypt, we can get free SSL certificates automatically. Simply tell Judas your phishing site’s domain and it’ll do the rest.
Proxy Support
Judas is able to use a HTTP or SOCKS5 proxy. You can hide requests from your target using a proxy, log them in case a client wants to see what exactly you took, get an IP address close to the target and much more. You can do multiple of these at once with proxychains.
HTTP Request Header Rewriting
Judas automatically rewrites HTTP request headers before sending them to the target website. It replaces the our phishing site in the Referer and Origin headers with an appropriate value and removes the user agent if the user didn’t send one to prevent Go’s default User Agent from showing up in logs and giving us away.
HTTP Response Header Rewriting
Judas automatically rewrites HTTP responses before they come back to the client. It removes any Content-Security Policy and anti-XSS headers on the response to prevent them from catching the phishing proxy and sending it to a report-URI (sorry blue team). It also rewrites the Location header to stop redirects with the full URL from sending the victim back to the original site.
Plugins
Real life is complicated. Maybe you need to phish a lot of people, or maybe you want to do something on behalf of a phished user because they have 2-Factor authentication enabled. Judas lets you use Go plugins to:
- Modify requests after they’ve been sent by the victim to enable attacks like replacing an admin’s request with a request to create a user for us
- Modify responses before they’re received by the victim so we can hide the results of attacks or hit victims with an exploit kit.
- Process request — response HTTP exchanges from victims in real time to programmatically extract sensitive information or store them in Azure CosmosDB to look at later.
RequestTransformers
A RequestTransformer is a function in a Go plugin named “RequestTransformer” that modifies an http.Request from a victim in place before it’s sent to the target. It should be fast so users don’t get suspicious or turned off by delays. You can use them to hijack legitimate requests. For example, a RequestTransformer could replace an admin users’s request with one that creates a user for us to gain access to protected systems.
ResponseTransformers
A ResponseTransformer is a function in a Go plugin named “ResponseTransformer” that modifies an http.Response from a target in place before it’s received by the victim. You can use them to hide what you’ve done from a target, or hit victims with an exploit kit.
Listeners
A listener runs in its own goroutine and receives request — response HTTP exchanges from victims in real time to allow us to extract sensitive information. The plugin loader looks for a function called “New” that returns a Judas Listener in a Go plugin.
Using Plugins
Once you’ve made a plugin, compile it and load it using command line arguments. Multiple plugins can be loaded be separating the plugin file paths with colons (“:”). There’s an example plugin with all 3 operations implemented on Judas's Github page.
Get Judas on Github
Judas’s source code is on Github. It’s MIT licensed, so feel free to modify it, fork it or whatever you see fit to do with it. Just don’t use it for crime. I’m not responsible for anything illegal you do with Judas, and I will laugh at you when cybercrime authorities in your country break your door down. Use your skills to make the world a better place instead of spreading misery.